RFID (radio frequency identification)
What is RFID (radio frequency identification)?
RFID (radio frequency identification) is a form of wireless communication that incorporates the use of electromagnetic or electrostatic coupling in the radio frequency portion of the electromagnetic spectrum to uniquely identify an object, animal or person.
How does RFID work?
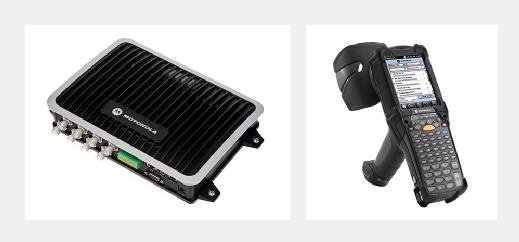
Every RFID system consists of three components: a scanning antenna, a transceiver and a transponder. When the scanning antenna and transceiver are combined, they are referred to as an RFID reader or interrogator. There are two types of RFID readers -- fixed readers and mobile readers. The RFID reader is a network-connected device that can be portable or permanently attached. It uses radio waves to transmit signals that activate the tag. Once activated, the tag sends a wave back to the antenna, where it is translated into data.
The transponder is in the RFID tag itself. The read range for RFID tags varies based on factors including the type of tag, type of reader, RFID frequency and interference in the surrounding environment or from other RFID tags and readers. Tags that have a stronger power source also have a longer read range.
What are RFID tags and smart labels?
RFID tags are made up of an integrated circuit (IC), an antenna and a substrate. The part of an RFID tag that encodes identifying information is called the RFID inlay.
There are two main types of RFID tags:
- Active RFID. An active RFID tag has its own power source, often a battery.
- Passive RFID. A passive RFID tag receives its power from the reading antenna, whose electromagnetic wave induces a current in the RFID tag's antenna.
There are also semi-passive RFID tags, meaning a battery runs the circuitry while communication is powered by the RFID reader.
Low-power, embedded non-volatile memory plays an important role in every RFID system. RFID tags typically hold less than 2,000 KB of data, including a unique identifier/serial number. Tags can be read-only or read-write, where data can be added by the reader or existing data overwritten.
The read range for RFID tags varies based on factors including type of tag, type of reader, RFID frequency, and interference in the surrounding environment or from other RFID tags and readers. Active RFID tags have a longer read range than passive RFID tags due to the stronger power source.
smart labels are simple RFID tags. These labels have an RFID tag embedded into an adhesive label and feature a barcode. They can also be used by both RFID and barcode readers. Smart labels can be printed on-demand using desktop printers, where RFID tags require more advanced equipment.
What are the types of RFID systems?
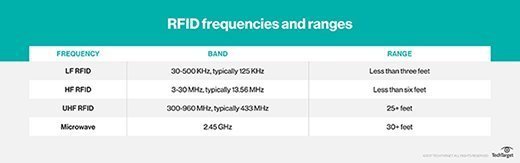
There are three main types of RFID systems: low frequency (LF), high frequency (HF) and ultra-high frequency (UHF). Microwave RFID is also available. Frequencies vary greatly by country and region.
- Low-frequency RFID systems. These range from 30 KHzto 500 KHz, though the typical frequency is 125 KHz. LF RFID has short transmission ranges, generally anywhere from a few inches to less than six feet.
- High-frequency RFID system These range from 3 MHzto 30 MHz, with the typical HF frequency being 13.56 MHz. The standard range is anywhere from a few inches to several feet.
- UHF RFID systems. These range from 300 MHz to 960 MHz, with the typical frequency of 433 MHz and can generally be read from 25-plus feet away.
- Microwave RFID systems. These run at 2.45 Ghzand can be read from 30-plus feet away.
The frequency used will depend on the RFID application, with actual obtained distances sometimes varying from what is expected. For example, when the U.S. State Department announced it would issue electronic passports enabled with an RFID chip, it said the chips would only be able to be read from approximately 4 inches away. However, the State Department soon received evidence that RFID readers could skim the information from the RFID tags from much farther than 4 inches -- sometimes upward of 33 feet away.
If longer read ranges are needed, using tags with additional power can boost read ranges to 300-plus feet.
RFID applications and use cases
RFID dates back to the 1940s; however, it was used more frequently in the 1970s. For a long time, the high cost of the tags and readers prohibited widespread commercial use. As hardware costs have decreased, RFID adoption has also increased.
Some common uses for RFID applications include:
- pet and livestock tracking
- inventory management
- asset tracking and equipment tracking
- inventory control
- cargo and supply chain logistics
- vehicle tracking
- customer service and loss control
- improved visibility and distribution in the supply chain
- access control in security situations
- shipping
- healthcare
- manufacturing
- retail sales
- tap-and-go credit card payments

RFID vs. barcodes
Using RFID as an alternative for barcodes is increasing in use. RFID and barcode technologies are used in similar ways to track inventory, but there are some important differences between them.
| RFID tags | Barcodes |
| Can identify individual objects without direct line of sight. | Direct line of sight required for scanning. |
| Can scan items from inches to feet away, depending on type of tag and reader. | Require closer proximity for scanning. |
| Data can be updated in real time. | Data is read-only and can't be changed. |
| Require a power source. | No power source needed. |
| Read time is less than 100 milliseconds per tag. | Read time is half a second or more per tag. |
| Contain a sensor attached to an antenna, often contained in a plastic cover and more costly than barcodes. | Printed on the outside of an object and more subject to wear. |
RFID vs. NFC
Near-field communication (NFC) enables data to be exchanged between devices by using short-range, high-frequency wireless communication technology. NFC combines the interface of a smart card and reader into a single device.
| Radio frequency ID | Near-field communication |
| Uni-directional | Bi-directional |
| Range up to 100 m | Range less than 0.2 m |
| LF/HF/UHF/Microwave | 13.56 MHz |
| Continuous sampling | No continuous sampling |
| Bit rate varies with frequency | Up to 424 Kbps |
| Power rate varies with frequency | <15 milliamperes |
RFID challenges
RFID is prone to two main issues:
- Reader collision. Reader collision, when a signal from one RFID reader interferes with a second reader, can be prevented by using an anti-collision protocol to make RFID tags take turns transmitting to their appropriate reader.
- Tag collision. Tag collision occurs when too many tags confuse an RFID reader by transmitting data at the same time. Choosing a reader that gathers tag info one at a time will prevent this issue.
RFID security and privacy
A common RFID security or privacy concern is that RFID tag data can be read by anyone with a compatible reader. Tags can often be read after an item leaves a store or supply chain. They can also be read without a user's knowledge using unauthorized readers, and if a tag has a unique serial number, it can be associated to a consumer. While a privacy concern for individuals, in military or medical settings this can be a national security concern or life-or-death matter.
Because RFID tags do not have a lot of compute power, they are unable to accommodate encryption, such as might be used in a challenge-response authentication system. One exception to this, however, is specific to RFID tags used in passports -- basic access control (BAC). Here, the chip has sufficient compute power to decode an encrypted token from the reader, thus proving the validity of the reader.
At the reader, information printed on the passport is machine-scanned and used to derive a key for the passport. There are three pieces of information used -- the passport number, the passport holder's birth date and the passport's expiration date -- along with a checksum digit for each of the three.
Researchers say this means passports are protected by a password with considerably less entropy than is normally used in e-commerce. They key is also static for the life of the passport, so once an entity has had one-time access to the printed key information, the passport is readable with or without the consent of the passport bearer until the passport expires.
The U.S. State Department, which adopted the BAC system in 2007, has added an anti-skimming material to electronic passports to mitigate the threat of undetected attempts to steal users' personal information.
RFID standards
There are several guidelines and specifications for RFID technology, but the main standards organizations are:
- International Organization for Standardization (ISO)
- Electronics Product Code Global Incorporated (EPCglobal)
- International Electrotechnical Commission (IEC)
Each radio frequency has associated standards, including ISO 14223 and ISO/IEC 18000-2 for LF RFID, ISO 15693 and ISO/IEC 14443 for HF RFID, and ISO 18000-6C for UHF RFID.
Next-generation RFID use
RFID systems are becoming increasingly used to support internet of things deployments. Combining the technology with smart sensors and/or GPS technology enables sensor data including temperature, movement and location to be wirelessly transmitted.