smart sensor
What is a smart sensor?
A smart sensor is a device that takes input from the physical environment and uses built-in compute resources to perform predefined functions upon detection of specific input and then process data before passing it on.
Smart sensors enable more accurate and automated collection of environmental data with less erroneous noise among the accurately recorded information. These devices are used for monitoring and control mechanisms in a variety of environments, including smart grids, battlefield reconnaissance, exploration and many science applications.
The smart sensor is also a crucial and integral element in the internet of things. IoT technology makes it possible to provide a unique identifier for almost anything and to transmit data from or about those things over the internet or a similar sensor network. One implementation of smart sensors is as components of a wireless sensor and actuator network, which can have thousands of nodes. Each node is connected to one or more other sensors and sensor hubs as well as to individual actuators.
Low-power mobile microprocessors typically provide compute resources in IoT environments. At a minimum, a smart sensor is made of a sensor, a microprocessor and wireless communication technology of some kind. The compute resources must be an integral part of the physical design. A sensor that just sends its data along for remote processing isn't considered a smart sensor.
This article is part of
Ultimate IoT implementation guide for businesses
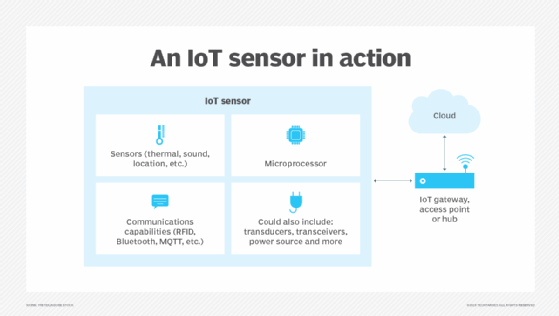
A smart sensor might also include several other components besides the primary sensor. These components can include transducers, amplifiers, excitation control, analog filters, analog-to-digital converters, and compensation that provides a built-in correction of less-than-ideal measurements or output. A smart sensor also incorporates software-defined elements that provide functions such as data conversion, digital processing and communication to external devices.
How do smart sensors work?
A smart sensor connects a raw base sensor to integrated computing resources that enable the sensor's input to be processed. The base sensor is the component that provides the sensing capability. It might be designed to sense heat, light or pressure. Often, the base sensor will produce an analog signal from an application algorithm that must be processed before it can be used. This process is also called signal processing.
At this point, an intelligent sensor's integrated technology comes into play. In signal processing, an onboard microprocessor uses a technique called filtering to remove signal noise and convert the sensor's signal into a usable, digital format.
Smart sensor technology also contain integrated communications capabilities that let them connect to a private cloud computing environment or the internet. This lets them communicate with external devices.
What are smart sensors used for?
Smart sensors have many uses. They're commonly found in industrial environments and are the driving force behind Industry 4.0 and industrial automation, robotics and other advanced instrumentation.
Factories often use smart sensors for diagnostic purposes. Smart temperature sensors ensure machines aren't overheating, and vibration sensors monitor machines at risk of vibrating loose. Smart sensors also enable process control, such as monitoring a manufacturing process and making necessary adjustments so it can meet quality or production goals. These were once manual processes, but smart sensors have automated them.
Smart sensors also play a key role in the advancement of modern security systems. Thermal imaging sensors detect an intruder's body heat. Similarly, devices such as smart locks, motion sensors, and window and door sensors are commonly connected to a common network. This lets the security sensors work together to create a comprehensive picture of the current security status. They are frequently used in homes and industrial applications to detect various leaks.
What are the different types of smart sensors?
There are many types of special purpose sensors in use. Five main types of smart sensors are commonly used in industrial IoT environments:
- Level sensors. These are used to measure the volume of space taken up in a container. A vehicle's fuel gauge might be connected to a level sensor that monitors the level of fuel in the tank.
- Temperature sensors. These monitor a component's temperature so a corrective action can be taken if the temperature gets too high or low. For example, in an industrial setting, a temperature sensor is used to ensure machinery doesn't overheat.
- Pressure sensors. These are used to monitor the pressure of gases or fluids in a pipeline. A sudden drop in pressure might indicate a leak or a flow control system issue.
- Infrared sensors. These are used in thermal imaging cameras and noncontact infrared thermometers are used for temperature monitoring. Other infrared sensors are optical sensors tuned to a frequency that helps them see light in the infrared spectrum. These sensors are used in medical equipment, such as pulse oximetry devices, and in electronic devices designed for remote control operation.
- Proximity sensors. These are used to detect the location of a person or object in relation to the sensor. In retail environments, proximity sensors can track customer movements throughout the store.
Other smart sensors can monitor electrical power consumption; vibration, such as in the case of factory equipment; humidity; moisture; and light.

What are the advantages and disadvantages of smart sensors?
Smart sensors come with a range of benefits, but they also have challenges and drawbacks.
Smart sensor advantages
The advantages of smart sensors are most prominent when they're used for data collection in austere or remote locations. The following advantages depend on deploying the right type of sensor where they're most needed:
- Energy efficiency and sustainability. A smart sensor can be programmed to be highly sensitive or receptive to even slight changes in surrounding conditions, such as temperature, humidity, moisture or acoustics. These highly accurate and reliable measurements provide a level of monitoring and data that collection can contribute to energy efficiency and sustainability efforts.
- Access to data in difficult environments. Smart sensors can collect data in remote places where it would be difficult or dangerous for people to go. Remotely operated, wireless smart sensors are particularly helpful in challenging environments.
- High performance. Smart sensors can collect data with consistency and speed when real-time data is needed.
- Built-in analytics and processing. Unlike traditional sensors, smart sensors feature certain built-in analytics and processing capabilities of the signals and data they receive, leading to increased efficiency as they require less outside analytics tools or resources.
Smart sensor disadvantages
Smart sensor developers have consistently upgraded their offerings to address longstanding drawbacks and will continue to do so in the future. That said, it may be a while before the current disadvantages of these devices are addressed:
- Susceptibility to tempering and hacking. Malicious actors, especially those looking to access collected data meant for private use, can do so if a device's cybersecurity measures are insufficient.
- Costs. Many devices are cost-prohibitive, and the cost of additional upkeep that will be required over time can also likely be expensive.
- Maintenance. Sensors at some point require recalibration or upgrades because of data latency or other issues. Ones located in remote settings or challenging environments can be difficult and costly to reach.
- Expertise. Smart sensor systems might require levels of IT expertise not all organizations have. New hires or training could be needed.
- Meeting requirements for IoT deployments. Whether in a smart home or an industrial setting, other factors must be taken into consideration before deploying IoT devices, like the power consumption required, the need for stable online connectivity and the ability to handle higher volumes of data.
How are smart sensors different from base sensors?
Smart sensors include an embedded Digital Motion Processor (DMP), whereas base sensors don't include one. A DMP is a microprocessor that's integrated into the sensor. It lets the sensor perform onboard processing of the sensor data. This might mean normalizing the data, filtering noise from electrical signals or performing other types of signal conditioning. In any case, a smart sensor performs data conversion digital processing prior to any communication to external devices.
A base sensor is simply a sensor that isn't equipped with a DMP or other compute resources that would let it process data. Whereas a smart sensor produces output that is ready to use, a base sensor's output is raw and must typically be converted into a usable format.
Smart sensors are generally preferred over base sensors because they include native processing capabilities. Even so, there are situations where it might be more advantageous to use a base sensor. If an engineer is designing a device and needs complete control over sensor input, then a base sensor would be preferable. Base sensors also cost less than smart sensors because they contain fewer components.
Although smart sensors are most often associated with industrial equipment, IoT couldn't exist without them. Learn more about the uses and benefits of smart sensors for IoT.







