thing (in the internet of things)
What is a thing (in the internet of things)?
A thing, in the context of the internet of things (IoT), refers to any entity such as a device that forms a network and can transfer data with other devices over the network. In an IoT network, each thing has a unique identifier, might be part of an embedded system, and can collect and share data with minimal or no human intervention.
The role of things in IoT
IoT is composed of millions of things that are connected to each other, can share and upload data to the internet, and can share data with other things. Most things are embedded devices that can communicate with each other and the internet -- or an intranet. Some things, such as door locks, can perform their tasks mechanically. Others, such as washing machines, have built-in electrical circuitry. And some, such as smart cars, have computing capabilities. Some things in IoT are hardware devices while others are software products.
Things in IoT are interconnected and form part of a larger ecosystem, which lets them collaborate with each other to carry out specific tasks. They can acquire data from their external environment, process it and yield insights that help human users draw conclusions and make decisions.
The increasing prevalence of digitization, advancements in wireless technology and the increasing miniaturization of computer components such as IoT sensors and processors makes it possible to develop and extend an IoT network or system for almost anything imaginable.
What makes a thing smart?
IoT networks consist of multiple smart things that can "talk" to each other. Whether it's cars or kitchen appliances, thermostats or baby monitors, shipping containers or mobile phones, what makes these things "smart" is seamless communication achieved with embedded sensors, communication technology and the internet. These various elements come together in an IoT network or ecosystem to collect information and present it in a useful way to end users. Some smart things can also process the information and use it to perform basic actions based on the underlying application and the intended user's requirements.
Smart things are not smart because they are sentient, but because they have some external measuring capacity and are powered by connectivity technology. It is this combination that allows the exchange of data between the thing and its environment, the thing and one or more users, and the thing and other IoT or non-IoT systems. Some things can also collect feedback -- for example, from human users -- and then process it to improve their own performance and better meet user expectations or requirements.
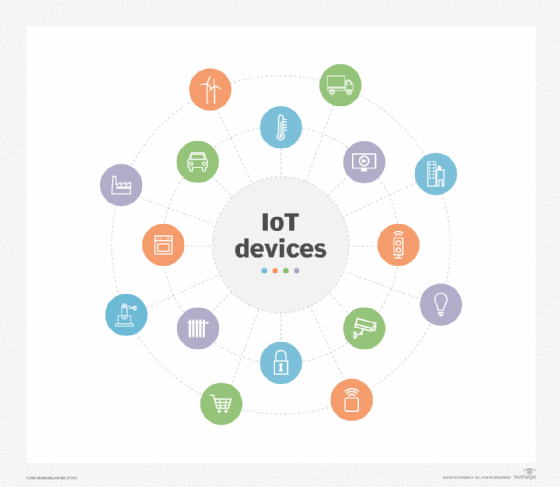
Examples of things in IoT
In an IoT network, a thing could be a dedicated computing device such as a PC, laptop, smartphone or tablet. In addition to these devices, the list of potential things is almost unlimited. It could be a home thermostat, an internet-connected car, a smart refrigerator, a drone, farming equipment, a freight container or many more things.
Things in IoT also encompass wearable devices such as smart watches and other devices that can monitor bodily functions and send data about these functions over the internet. Increasingly, real-world applications in areas including supply chain management, logistics and agriculture are relying on things such as digital ledgers, real-time monitoring, data pipelines and irrigation systems. All these are also things because they are connected with other things and to the internet, and they have data collection and data sharing capabilities.
Technological enablers of communication between things
Many things in IoT communicate with each other over the public internet using internet protocols or some proprietary protocols. These protocols enable connections between sensors and the internet, the cloud and other things for communication and data transfer. Internet-connected IoT systems usually involve devices such as mobile phones, gateway devices and embedded cellular connections.
In many IoT systems, inter-thing communication does not happen over the internet. Even so, an internet connection is present at some point -- for example, when a user's mobile device is connected to the internet.
Cloud computing platforms such as Amazon Web Services and Microsoft Azure also enable communications among IoT things. In addition, they enable the setup and scaling of IoT systems, with the platform and platform provider managing all the things in the system. As a result, businesses and consumers don't have to manage the system or worry about aspects including its scalability, security, integrations or maintenance.
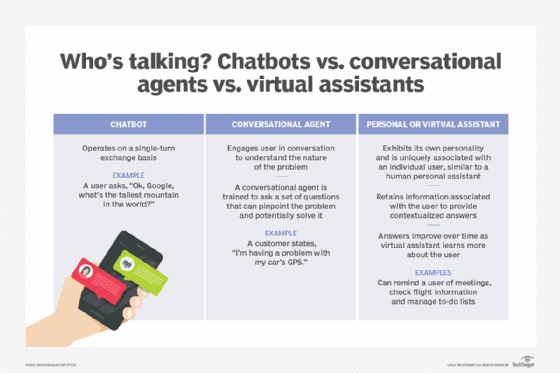
The emergence of technologies including artificial intelligence (AI), machine learning and analytics also enables advancements in IoT systems. These technologies allow things to access varied and vast amounts of data, as well as help users gather insights faster and make data-driven decisions. In addition, conversational AI and natural language processing applications power some things that support the IoT system's intended functions and use cases. A ubiquitous example of such things are digital personal assistants such as Amazon's Alexa or iPhone's Siri. These consumer-facing AI tools are different from two other categories of virtual assistants: chatbots and conversational agents.
The importance of security for things in IoT
Things enable smart computing, smart communications and smart decision-making. However, their flexibility and connectivity also create security risks, including cyber attacks. Since many things are connected to the public internet and have known vulnerabilities, attackers can easily exploit these to attack an IoT device and even entire IoT networks.
Hackers can also hijack a connected device and use it to attack and then control a disconnected system. In 2015, security researchers Charlie Miller and Chris Valasek showed how attackers could take over a smart car's internal computer network to compromise many of the vehicle's functions, such as its door locks, dashboard, steering, transmission and even brakes.
Such risks could emerge in many kinds of things in IoT, creating a growing attack surface for threat actors to exploit. Many things use communication technologies such as Bluetooth and Wi-Fi that can contain known vulnerabilities and increase the attack risk. Miller and Valasek also showed how attackers using just a cellphone could take advantage of a vulnerable cellular network to attack smart things. For all these reasons, it's vital for the manufacturers and users of things in IoT to make security a priority and close as many attack pathways as possible.






